AARP Hearing Center
The Thing About the Internet of Things
By Neal Walters, February 12, 2015 10:07 AM
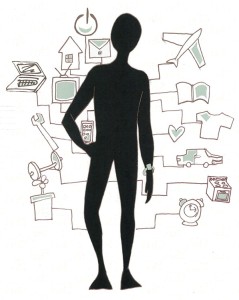
We’ve been hearing a lot lately about the “Internet of Things” (IoT). Often, the discussion revolves around issues associated with data privacy and cybersecurity.
So what is the IoT and what’s all the fuss about?
IoT refers to the ever-expanding array of devices that can communicate to external networks. While we all realize our computers and smartphones are connecting to the outside world, more and more devices such as fitness trackers, cameras, cars and thermostats are doing so as well.
>> Catch up on the latest personal technology news and resources
And how big will the IoT become? CISCO estimates there will be 50 billion connected devices by the year 2020.
Privacy experts worry that the detailed data collected by these devices will allow companies to create comprehensive behavioral profiles of people. Profiles that eventually could become part of credit, insurance or employment decisions.
Security experts express a different set of worries. They note that connected devices are vulnerable to hacking, which could allow hackers to take control of the device. For example, researchers are able to successfully hack into cars, thereby allowing them to take control of crucial systems such as steering and brakes.
Another concern is that hackers will use security vulnerabilities in connected devices to spy on the device owners. Recently, hackers have exploited security weaknesses in baby monitors and home security cameras, thereby allowing the hackers to view and hear people in their own homes.
Amid the growth of connected devices, the Federal Trade Commission (FTC) released a report addressing some of the security and privacy concerns associated with the IoT.
The report recommends best practices to improve the security of connected devices. In addition, data minimization — limiting the amount of data collected by the devices — is also encouraged to help protect privacy. Notably, the report calls for a voluntary self-regulatory approach and not creating any IoT-specific legislation.
However, the report raises a number of concerns.
Some security and privacy advocates fret that a voluntary self-regulatory regime won’t suffice. After all, this approach has proven unsuccessful in the FTC’s high-profile quest to create a Do-Not-Track list to give consumers a way to control their online privacy. By not requiring companies to use the best practices, there’s no guarantee that companies will follow them.
>> 10 Ways to Protect Yourself From Identity Theft
Further, the FTC call to protect consumer privacy by minimizing data collection via IoT devices is meeting resistance from within the FTC. Two FTC commissioners criticized the report for its failure to use a cost-benefit analysis before recommending data minimization. In particular, they note limiting data collection to avoid hypothetical future harms might result in companies missing insights that could later prove valuable to both businesses and customers.
As a result, it’s hard to say whether the FTC report will have any meaningful impact in creating a more secure and private IoT. Because the report stops short of requiring greater security and privacy, some experts think it is unlikely to have a significant impact.
While the IoT continues to grow and becomes further integrated into our daily lives, consumers can be forgiven for worrying about the associated security and privacy issues. In the end, a voluntary best practices approach might well fall short of providing necessary protections. Legislators and regulators may need to mandate security and privacy protections to make the IoT work for both consumers and businesses.
Image: Jasmyne Jackson
Neal Walters is a policy research senior analyst for the Economic and Consumer Security Team who publishes on topics including financial information privacy, identity theft, affordable home utilities, prepaid cards and credit reporting.
Also of Interest
- Once More Unto the Security Breach
- Common Sleep and Allergy Medications Linked to Dementia, Alzheimer’s
- AARP Foundation Tax-Aide: Get Free Help Preparing and Filing Your Taxes
- Join AARP: savings, resources and news for your well-being
See the AARP home page for deals, savings tips, trivia and more.